How to Protect Yourself from Cybercrime, the Darknet, and Online Threats
In today’s digital age, cybercriminals and darknet marketplaces pose serious threats to our online privacy and security.
Take for instance the recent takedown of Genesis Market, an illegal marketplace where hackers purchased “digital fingerprints” of breached computer systems. In early April 2023, federal agents arrested more than 100 people using the site in an outfit called “Operation Cookie Monster.” This emphasizes the importance of being careful with our sensitive data when using the internet.
What is cybercrime?
Cybercrime refers to any illegal activity that involves computers, networks, or the internet. As technology advances, so do the tactics of cybercriminals, who exploit vulnerabilities in digital systems to gain unauthorized access, steal sensitive information, or cause harm. Cybercrime can take many forms, including hacking, identity theft, phishing, malware attacks, and online scams.
Why it’s important to protect your information online
Our lives are increasingly digital. This raises the risk of our personal information being stolen, sold, or misused – greater than ever before. Cybercriminals can access our financial data, personal details, and even social media accounts, leading to identity theft and potential financial losses.
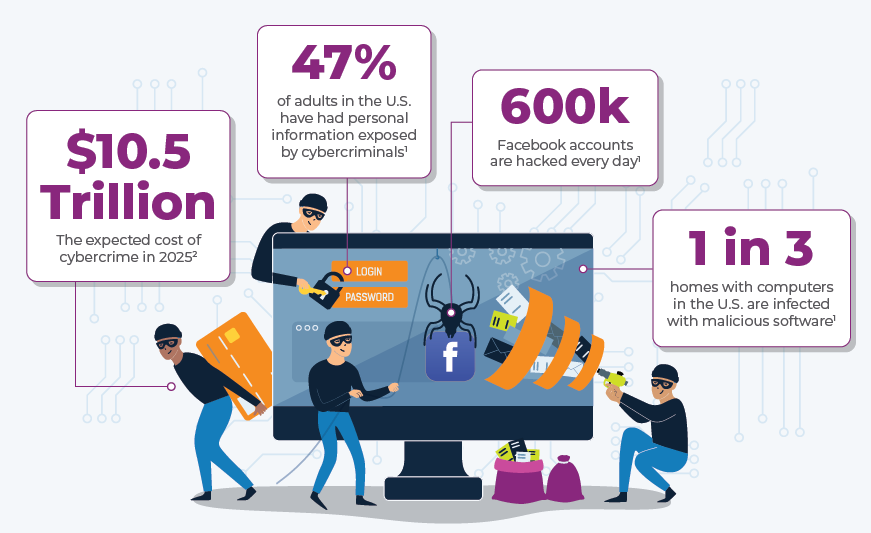
You might be startled by the following cybercrime statistics:
- 47% of adults in the U.S. have had personal information exposed by cybercriminals
- 1 in 3 homes with computers in the U.S. are infected with malicious software
- 600k Facebook accounts are hacked every day
- The cost of cybercrime is expected to reach $10.5 trillion in 2025
That’s why it’s crucial to prioritize your digital safety and take proactive measures to prevent cyberattacks. While these crimes and theft cannot be avoided completely, having security and protection in place is a crucial step toward being prepared and staying safer online.
Who are the victims of cybercrime?
Cybercrime is an ageless, genderless crime that knows no bounds or borders; it can happen to anyone, anywhere.
You may be wondering if cybersecurity tools and services are necessary.
Perhaps you’re familiar with phishing or already monitor your children’s screen time. Our policy is, it’s better to be safe than sorry, and there’s more than one reason to keep yourself, your family, and your data protected.
According to the U.S. Cybersecurity & Infrastructure Security Agency (CISA), about 65% of Americans who go online have received at least one online scam offer. CompTIA reports that more than any other country in the world, the U.S. is the target of 46% of global cyberattacks.
If you’re younger, you may think because you grew up with the internet, you know how to protect yourself. But consider the facts.
CISA found that about 44% of Millennials were victims of online crime in the last year, and about 31% of the generation shares passwords – more than any other age group.
In a recent study from the National Cybersecurity Alliance and CybSafe, 47% of Gen Z participants believed staying secure online was easy, but their group reported higher cybercrime victimization rates than older generations. Gen Z are the most likely victims of phishing and cyberbullying, according to the study. They also had the second-highest rates for identity theft and romance scams, with Millennials ranking first overall.
Who are cybercriminals and how do they steal your information?
Cybercriminals are individuals or groups who use technology to commit illegal activities, often with the intent of stealing sensitive information or causing harm.
They exploit the dark web, a part of the internet that can only be accessed using special software like the Tor browser, which offers anonymity and makes it an ideal place for criminal activities such as selling stolen data, illegal drugs, and other items.
Hackers employ various tactics to obtain your personal information, including:
- Phishing emails: Deceptive emails that appear to be from legitimate sources, like banks or online services. They often contain links that direct you to fake websites, where you are asked to provide sensitive information such as login credentials or personal details.
- Social engineering: This tactic involves manipulating people into divulging confidential information. For example, a hacker may impersonate a trusted individual, such as a coworker or family member, to trick you into sharing passwords or other sensitive data.
- Exploiting security vulnerabilities: Cybercriminals are constantly searching for weaknesses in software and network security. When they find a vulnerability, they exploit it to gain unauthorized access to systems and steal valuable information.
- Malware: Malicious software, or malware, can be disguised as seemingly harmless files or applications. Once installed on your device, it can steal your data, monitor your activity, or even take control of your system.
- Man-in-the-middle (MITM) attacks: Hackers intercept communications between two parties, often on public Wi-Fi networks, to steal sensitive information or alter the contents of the messages.
- Password attacks: Hackers use various methods to crack passwords, such as guessing common phrases, using a dictionary attack (trying every word in a dictionary), or employing brute force attacks (testing all possible combinations)
Understanding how these bad actors operate and how they can access your information is a crucial step in protecting your digital life.
How to find out if your information has been stolen or sold
One way to check if your data has been compromised is by using the website Have I Been Pwned. This site lets you enter your email address to see if it has been part of any known data breaches.
Another way to keep tabs on your digital information is to check your credit score – any significant changes could be a sign that your identity has been stolen.
If your information has been compromised, it’s essential to take immediate action by changing your passwords and securing your accounts.
How to protect yourself from cybercrime
To enhance your internet security and safeguard your online privacy, consider these steps:
- Use strong, unique passwords for all your accounts and enable two-factor authentication whenever possible.
- Keep your software, operating system, and antivirus up-to-date.
- Be cautious about the links you click and the attachments you open in emails.
- Use a VPN for secure browsing, especially when connecting to public Wi-Fi networks.
- Enable a firewall on your devices to prevent unauthorized access.
Taking these steps can help you mitigate the risks associated with having your information stolen or sold and provide a solid foundation for maintaining your online security.
How EarthLink Protect and EarthLink Protect+ can help
EarthLink has partnered with Norton to offer comprehensive cybersecurity packages, EarthLink Protect and EarthLink Protect+. Our premium online security features include :
- Real-Time Threat Protection: Advanced Norton Device Security keeps online threats like ransomware, viruses, spyware, and malware at bay
- Norton Secure VPN: Keep your connection private at home and on-the-go
- Dark Web Monitoring: Norton LifeLock patrols the dark web and alerts you if your personal information is found on the dark web
- LifeLock Identity Alert™ System: Receive instant updates when personal information such as your Social Security number, name, address, or date of birth are used on applications for credit and services that affect your credit
- Million Dollar Protection™ Package: Get reimbursed for funds stolen and coverage for personal expenses up to the limit of your plan if your identity is stolen
- Data Breach Notifications: Be prepared for corporate breaches, and get immediate notifications if your data is leaked in a large-scale attack
- Parental Controls: Let your kids surf the internet safely and securely
- PC SafeCam: Protect your computer’s webcam from spies, voyeurs, and criminals
- Password Manager: Manage your online credentials in one secure spot
By investing in a cybersecurity package like EarthLink Protect or EarthLink Protect+, you can ensure that your digital life remains safe from cybercriminals and darknet marketplaces.
Conclusion
In this digital age, it’s never been more important to prioritize your online privacy and internet security.
By understanding the risks and taking proactive steps to protect your information, you can enjoy the benefits of the digital age without the fear of cybercrime.
To further enhance your digital safety, consider EarthLink Protect or EarthLink Protect+ for a comprehensive cybersecurity solution. Call our internet experts to learn more today at 833-957-0229.